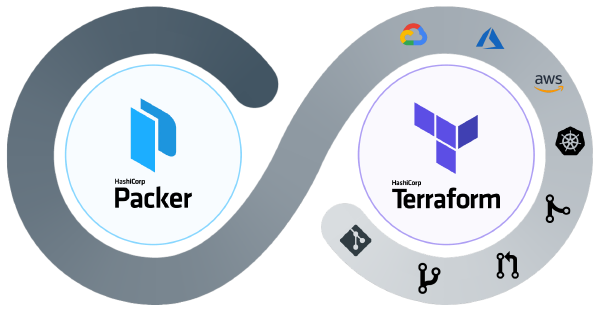
HashiCorp’s Terraform needs no introduction. It is all but the de facto vehicle for delivering cloud infrastructure, and for a good reason. What Terraform did for Multi-Cloud Infrastructure as Code, is precisely what Alkira does for the network. What happens when you use these two platforms together to deliver networking in and across clouds? If providing network services in code faster than ever before sounds interesting, this multi-part series is for you. Need a quick primer on Alkira? You can read up here.
A Scalable Foundation#
Troubleshooting networks that have been over-engineered can be tricky. Some of the most reliable networks I have worked in were also the most simple by design. Simple is easier to understand, automate, and scale. To begin this series, let’s deploy the following:
- A Segment for macro-segmentation; (We will deploy additional segments in a later post to demonstrate Partner and Acquisition connectivity scenarios)
- Groups for micro-segmentation; These will be used for policy enforcement once we start connecting cloud and on-premises networks
- A Billing Tag mapping to a hypothetical Line of Business (Let’s say Digital Transformation); Being able to bill specific app or product teams for network consumption is a game-changer
- An Internet Exit for users, sites, and clouds along with elastically scaled VM-Series Firewalls for our IPS, IDS, and ALG needs
Segmentation Layout#
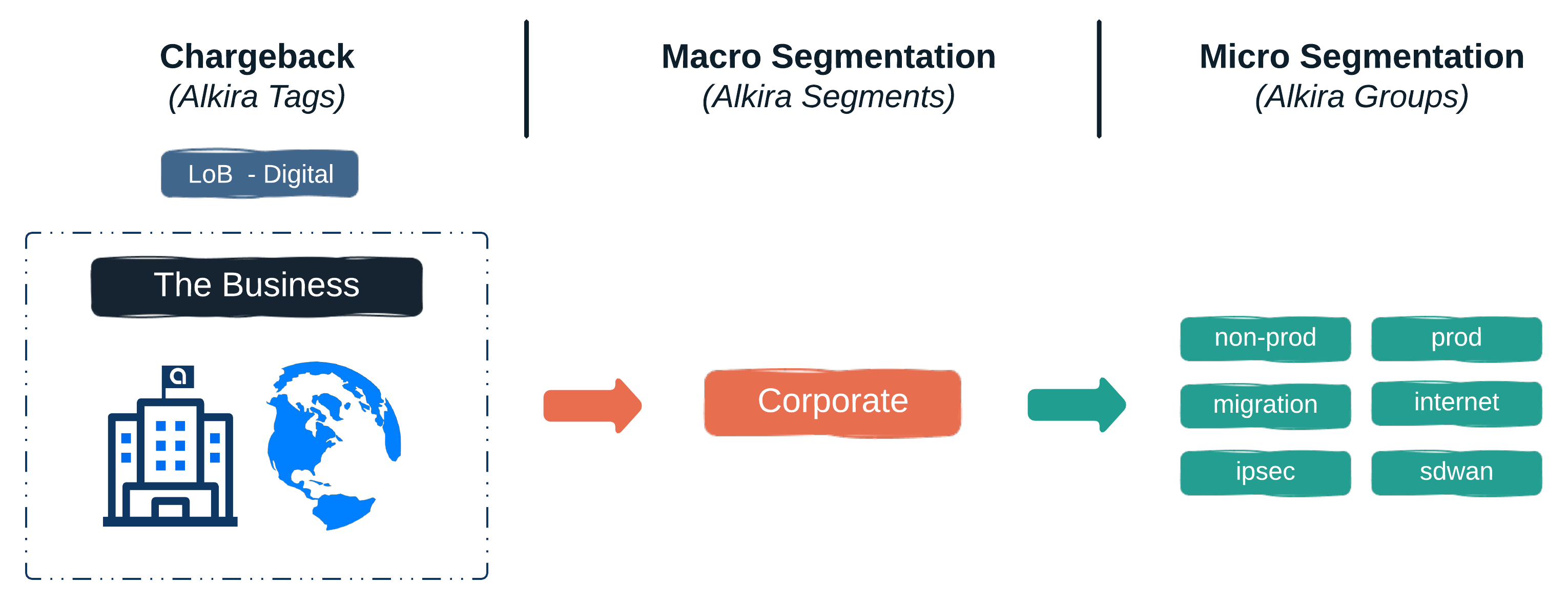
In Alkira, segments and groups are scaled globally, across clouds, and on-demand. To learn more about how Alkira handles segmentation, check out this design zone video.
Let’s Build!#
Segmentation#
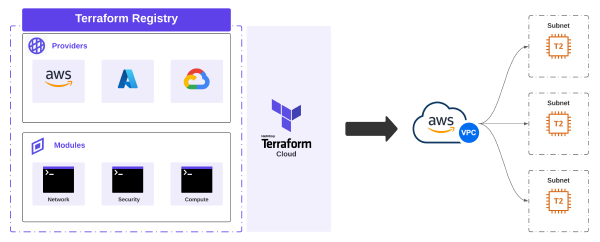
Alkira’s Terraform Provider makes it easy to build networking the DevOps way. The following snippet creates our segment and groups used for macro and micro segmentation.
alkira_segments.tf
| |
Internet Egress#
The following code will provision an Internet Connector with VM-Series Firewalls. These scale to real-time capacity demand while symmetrically steering application traffic using intent-based policies.
Internet, Intranet, and Private-Spoke security zones will be provisioned on the Firewalls with each zone mapping back to the corresponding Alkira Groups which provide the baseline for segmentation and policy
alkira_internet.tf
| |
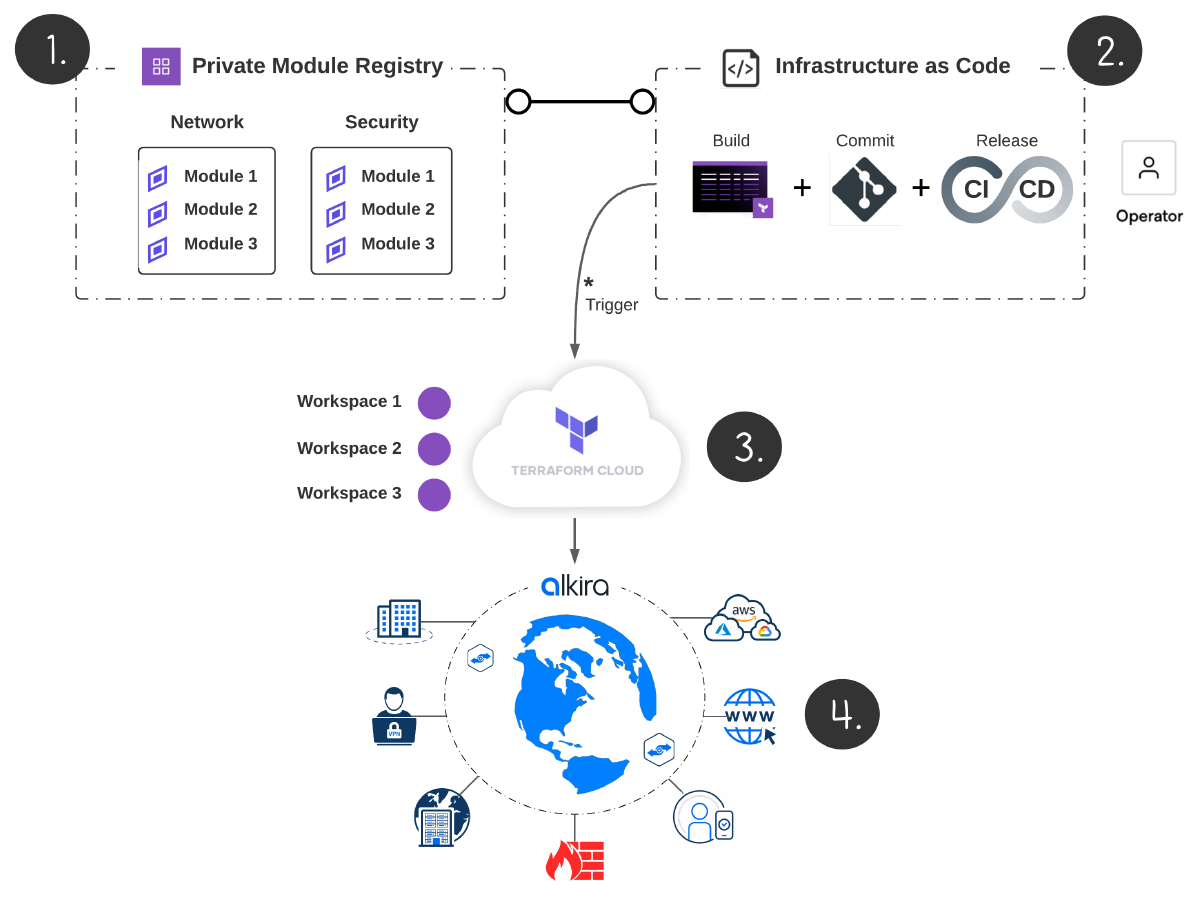
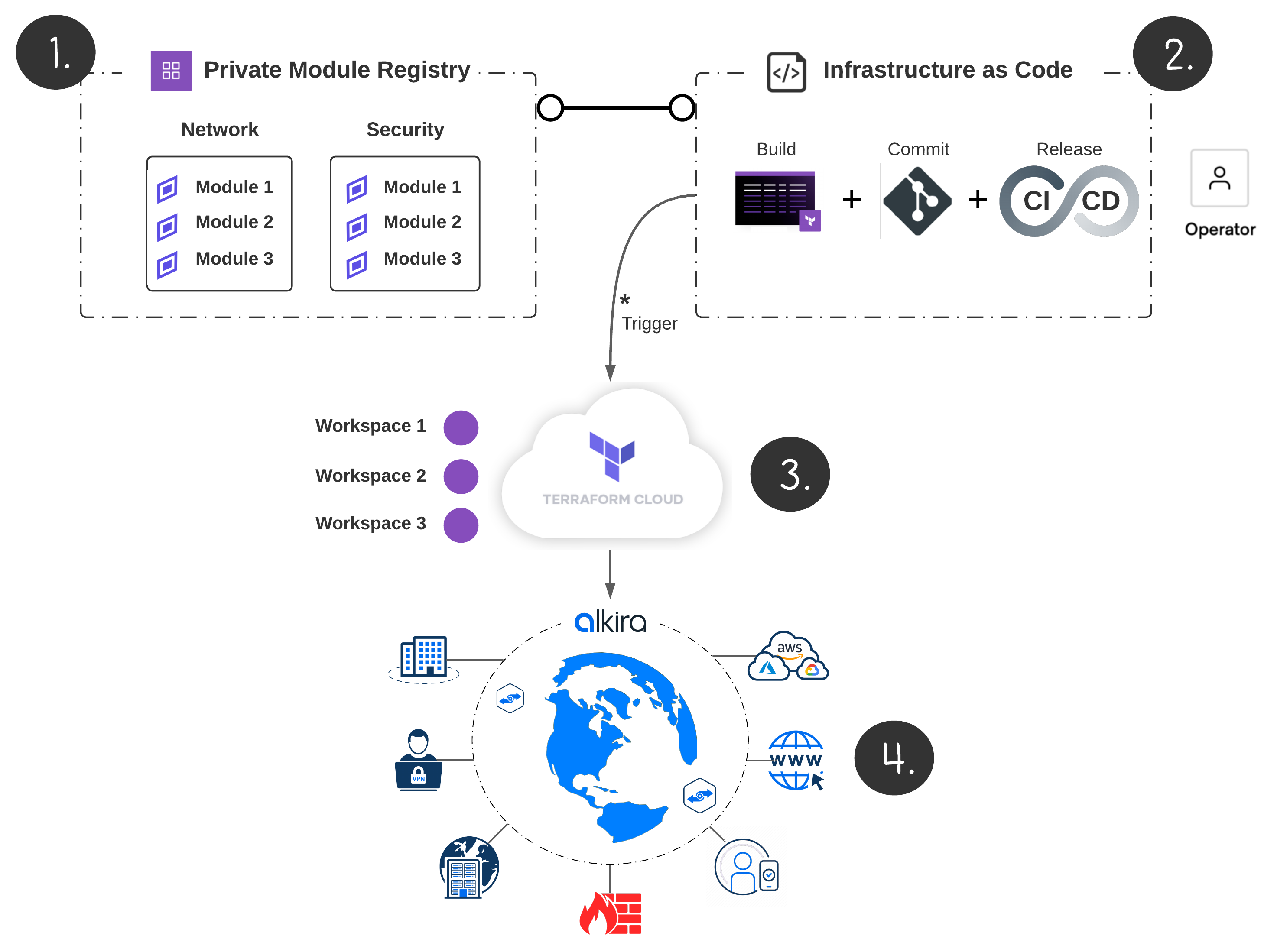
Provision On Pull Request#
I’m a big fan of Terraform Cloud. For this example, I have my infrastructure committed to Github with Terraform Cloud runs triggered automatically as changes get merged in version control.
Validation#
Alkira has a very refined interface which serves as a great visual aid to validate configuration and policy. As we add more infrastructure later in this series, we will use the UI to gain a greater perspective into each aspect of the network.
Conclusion#
The place where applications, data, and systems intersect is the network. Networks of the future must adapt and scale over time as businesses grow, markets change, and policies adapt. Elastic networking driven by automation is the future. In Part 2, we will connect a mix of AWS, Azure, and GCP networks to demonstrate just how easy Alkira can make the multi-cloud network experience, so stay tuned!