Anyone that has worked in tech knows that building greenfield is much easier than dragging along brownfield environments through a roller-coaster they aren’t ready for. Tools like Terraform make infrastructure-as-code a breeze, but what about all that infrastructure you already have provisioned? April Edwards, Cloud Advocate at Microsoft, recently posted a blog about Azure Terrafy, a new tool in preview which aims to simplify the process. You can find the original blog here. Let’s take it for a spin!
Terraform Import enables the importing of infrastructure today, but this only imports one resource at a time, and it’s on you to build the configuration files. Sounds time-consuming, right? When you are in the process of learning Terraform, having a tool that can import brownfield environments into state while also generating the HCL files, is extremely useful.
Installing Terrafy#
I installed it via go install github.com/Azure/aztfy@latest.
Building some Infra#
To kick off this little experiment, I will build some infrastructure in Azure using Terraform and then create a different project directory to test Terrafy in. If things go south, I don’t have to remove everything manually.
main.tf
| |
Running Terrafy#
I created an empty directory called terrafy-test for this exercise. Before running Terrafy, make sure azure-cli is installed and authenticated. If your running on macOS and use Homebrew, you can run brew update && brew install azure-cli and then az login.

Like a boss, I ran with defaults and didn’t bother reading any of the well-crafted README. Most of the resources were translated fine, but I noticed the virtual machines and storage accounts didn’t make it. When going through the setup, you will be able to cycle through and view all the resources available to import. If you see (Skip), that resource will indeed get skipped unless you update the resource type accordingly.
Was it Successful?#
Let’s test a few things before we ride off into the sunset. I did a terraform plan -refresh only, and also updated some resources, and everything looks good!
Some Thoughts#
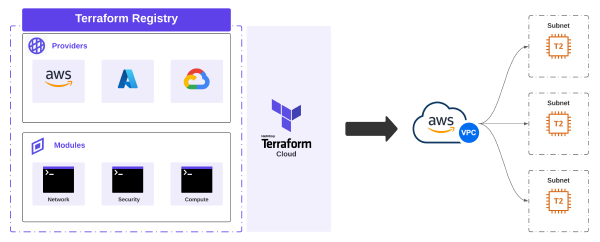
This is a great tool, especially in learning and adoption of infrastructure-as-code. The import process is scoped at the resource group level, which makes a lot of sense. Subscriptions would be the next level up, and that might get too messy. When Terrafy generates the infra-as-code files, it builds a provider.tf to source the azurerm details, and all the other configuration is generated in a monolithic main.tf file. This is the layout here:
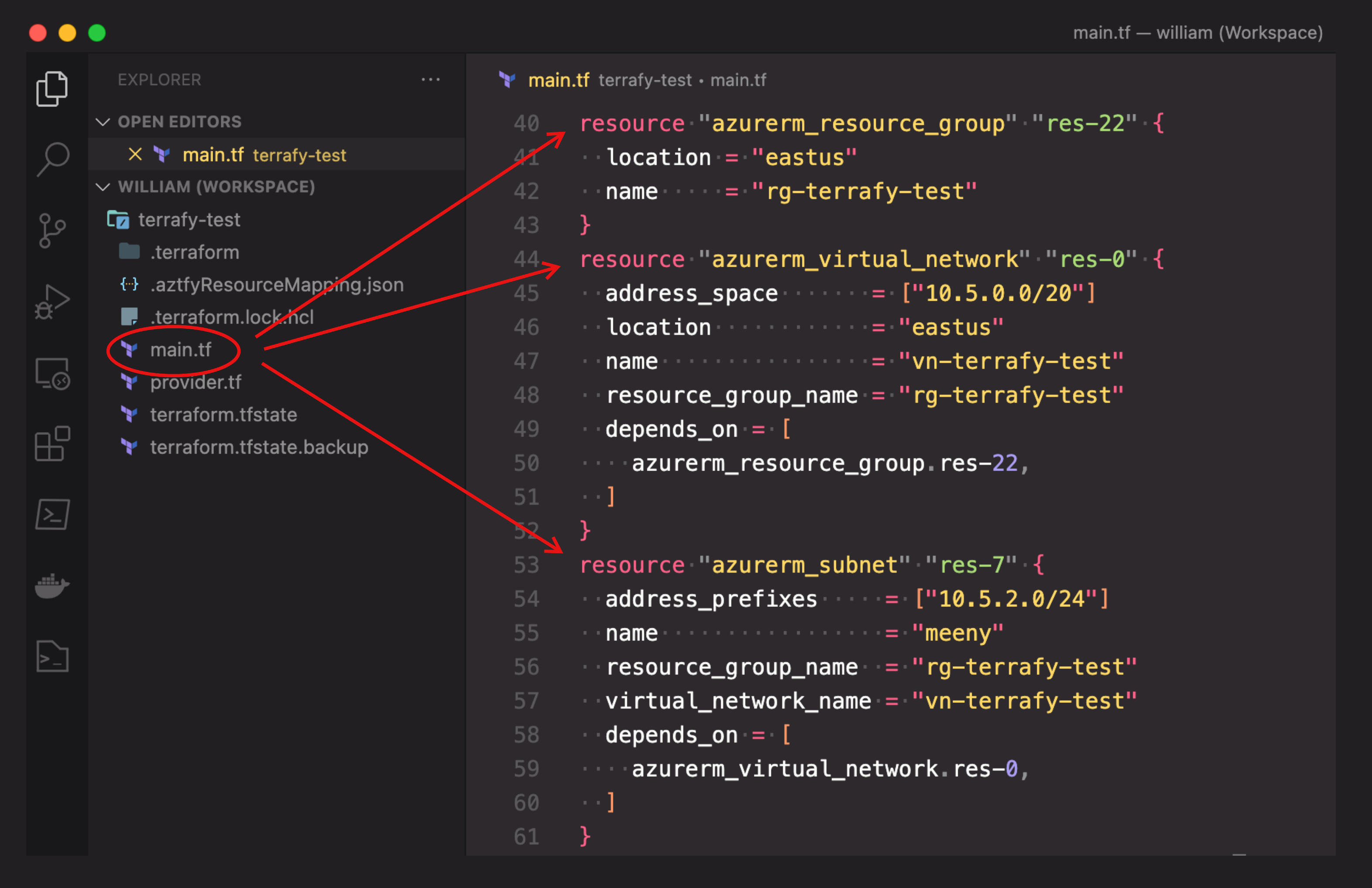
More Organization#
With infra-as-code, there is no easy button. To make things work at scale, things have to be organized. As a starting point, it would be neat to see Terrafy do more organization. Even something simple like breaking down infra into separate categories would be helpful.
An example of this would be taking resources like localNetworkGateways, networkSecurityGroups, and virtualNetworks and putting them into a separate file called network.tf as they all fall under Microsoft.Network when drilling down through azurerm.
Virtual Machines and all compute-related components would fall under Microsoft.Compute and would be in a different file called compute.tf. Organizing things in categories like this would make it easy to sift through larger imports.
Summary#
Terrafy is a great way to bring existing infrastructure into Terraform state. Installation and usage are simple, and the documentation is good. I think this tool will gain enough momentum that new features will come quickly, hopefully on the organization side. To learn more, visit the GitHub page. Happy building!